LACNIC Launches New Service for Detecting Open DNS Servers with IPv6 in the Region
27/02/2019
LACNIC has developed a new service for organizations and network administrators in the LAC region to verify whether the DNS servers they are using with IPv6 addresses are properly configured.
Developed by LACNIC WARP and the organization’s R+D department, this tool is freely available at the following link and provides a very simple way to check whether a DNS server is open.
While this service was under development, LACNIC conducted a survey through which the organization detected that 2.63% of the IPv6 DNS servers in Latin America and the Caribbean were open and vulnerable to cyberattacks.
The goal of the project was to identify the number of open IPv6 resolvers in the region, while also developing a series of recommendations to correct potential server configuration errors, said Darío Gómez, security analyst at LACNIC and one of the persons responsible for the initiative.
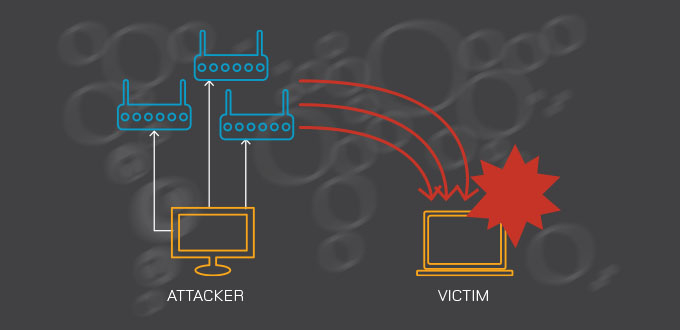
Gómez noted that the presence of open servers can have serious consequences, both for those who leave the service open as well as for Internet security in general. An open server can receive recursive queries and is therefore vulnerable to being used as a vector for amplification DDoS attacks, as a small query message allows obtaining a much larger response. LACNIC WARP has received multiple reports of incidents involving the vulnerability of open DNS servers in Latin America and the Caribbean.
During the initial phase of this research, the LACNIC team performed checks on reverse DNS server “D”, which converts IP addresses to domain names. This allowed them to identify the percentage of open servers in the region (2.63%). This study considered one and a half million weekly queries to reverse root server “D” managed by LACNIC. Compared to the other RIRs, LACNIC is the second most affected region, with similar numbers to those of ARIN (2.44%) and AFRINIC (2.36%). The region most affected by open resolver servers is APNIC (8.16%), while the percentage of incorrectly configured servers in the RIPE NCC region is practically insignificant (1%).
How to solve this problem. After determining the number of servers that are open and vulnerable to attacks, the LACNIC team developed the tool that will allow organizations and network administrators to automatically check their DNS configuration.
They also prepared a series of recommendations on how to re-configure open DNS servers.
In addition, LACNIC performs a weekly server check, notifies the organizations with DNS configuration errors and sends them the suggestions prepared by LACNIC.